Sponsored by IBM
Sponsored by IBM
Omdia Universe: Selecting a Global IT Security Services Provider
Sponsored by IronNet
Building a secure utility ecosystem with NDR and Collective Defense
Sponsored by BMC
Delivering Mainframe Services in the New Normal
Sponsored by Zoho Corp - ManageEngine
Exploring the Methodology of DDoS Attacks
Sponsored by Zoho Corp - ManageEngine
Combating Hacking Techniques: How to Defend Against DDoS, Ransomware, and Cryptojacking
Sponsored by Zoho Corp - ManageEngine
Tried and Tested Best Practices for Active Directory Security
Sponsored by Okta
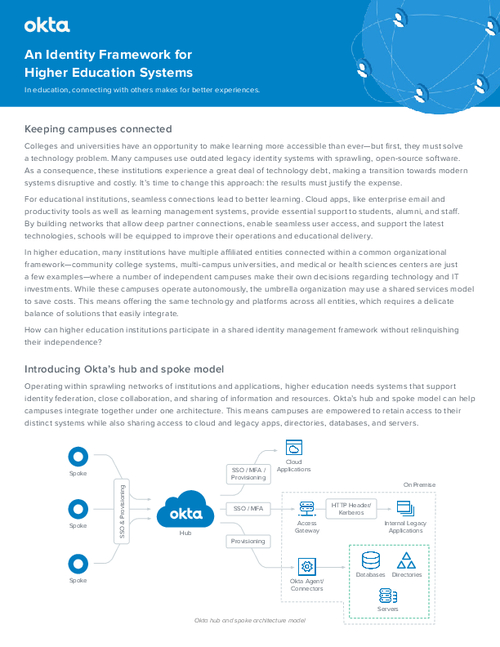
Identity Frameworks for Education Systems
Sponsored by Okta
Identity Frameworks for Higher Education Systems
Sponsored by Okta